As the cost of label manufacturing declines, the application of RFID technology will become more widespread, with a series of security and privacy issues. This paper introduces the security and privacy threats that RFID applications may generate, as well as several solutions for data protection. It describes a security threat in a hypothetical application, and mainly introduces a hierarchical privacy-based RFID privacy protection method.
Radio Frequency IdenTIficaTIon (RFID) technology is a technology that realizes contactless information transmission through electromagnetic coupling through electromagnetic coupling and achieves identification purposes through the transmitted information. Because it can realize automatic identification and information sharing conveniently and quickly, RFID technology has broad application prospects in the fields of transportation, warehousing management, electronic ticketing and electronic payment.
The system usually consists of a tag, a reader and a radio frequency network. The tag stores a certain format of electronic data, which is often used as a basis for identifying objects; the reader and the tag communicate information by an agreed communication protocol; the radio frequency network is mainly from the middle It consists of ONS (Object Name Service) and IS (InformaTIon Sever), providing instant information interaction. Figure 1 shows a simple RFID system architecture. The system works as follows:
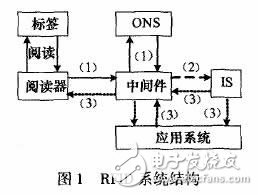
(1) The reader sends the tag information obtained by the query to the middleware, and the middleware converts the received tag code into an ONS readable code, and then requests the URL of the ONS by the converted code, and the ONS parses the corresponding code. The URL is sent back to the middleware.
(2) Using the obtained URL and tag information, the middleware queries Is, and Is finds matching information in the database.
(3) Through the middleware or application system, Is sends the queried information back to the reader.
1 RFID security and privacy threats1.1 RFID privacy threats
Privacy is the right of individuals to have their information inviolable. In RFID systems, RF waves can be transmitted through buildings or metals, allowing tags and readers to be embedded in any object; secondly, wireless communication between the reader and the tag, the channel eavesdropping problem is extremely serious; again, the tag Limited resources, encryption algorithm and access process is relatively simple; the above reasons allow attackers to have a large number of vulnerabilities to use, and the control of the tag allows the attacker to obtain real benefits, thereby increasing the security and privacy risks of the RFID system, below There are several common threats.
1) Tracking users carrying tags or when purchasing tagged items may leak personal information or expose their location because they are being monitored.
2) The label of the favorite threat product indicates the manufacturer, product type and other characteristics, and the customer's quality preference and personality characteristics are exposed when the customer purchases the product.
3) Layout threats Regardless of whether the user's identity is associated with a tag set, a specific tag pattern is formed around each person, and advertisers can use this layout to track customers.
4) Leakage Because the RFID system reads quickly, it can quickly scan all the goods in the supply chain and track changes, etc., and is used to steal trade secrets.
1.2 An idea of ​​RFID security threats
Compared to mid-high frequency RFID systems, supermarket UHF RFID systems operating at 800 MHz (Europe) / 900 MHz (US) have farther read distances and higher data rates. However, at these operating frequencies, radio frequency waves are easily absorbed by water or metal, and the main component of the human body is water. Radio frequency waves can cause harm to the human body. More importantly, when consumers purchase canned beverages and other products, they are due to radio frequency waves. Being absorbed makes communication between the reader and the tag no longer accurate, disrupting the normal payment process.
The following describes a scenario that poses a serious threat to the operation of a supermarket RFID system.
(1) Supermarkets have built RFID systems and implemented functions such as warehouse management and automatic charging of goods for sale. The readers used by supermarket managers can read and write commodity label data (requires access keys when writing label data), taking into account price adjustments. And other factors, the tag data must be able to read and write multiple times.
(2) Mobile RFID users themselves carry a reader embedded in a mobile phone or PDA, which can scan the labels of goods in the supermarket to obtain detailed information such as the manufacturer, date of manufacture and price of the product.
(3) By intercepting channel interception information, brute force cracking (using directional antennas and digital oscilloscopes to monitor the power consumption when the tag is read, determining when the tag accepts the correct password bit) or other human factors, the attacker gets the tag data. The required access key.
(4) Using the tag's access key, the attacker arbitrarily modifies the tag data, changes the price of the product, and even the "kill" tag causes the supermarket's product management and charging system to fall into chaos for personal gain.
2 data protection scheme1) After the self-destruction and dormant goods are purchased, the tag will be permanently invalid after receiving the “kill†command from the reader, but in the library or rental store, the tag must be valid during the usage period and cannot be “killed†at one time. Sleep is similar to self-destruction, but the sleep tag can be activated again after "wake up".
Edge Sealing Machine,Automatic Sealing Machine,Heat Sealing Machine,Automatic Edge Sealing Machine
Dongguan Yuantong Technology Co., Ltd. , https://www.ytbagmachine.com
